In what’s a continuing assault on the open source ecosystem, over 15,000 spam packages have flooded the npm repository in an attempt to distribute phishing links.
“The packages were created using automated processes, with project descriptions and auto-generated names that closely resembled one another,” Checkmarx researcher Yehuda Gelb said in a Tuesday report.
“The attackers referred to retail websites using referral IDs, thus profiting from the referral rewards they earned.”
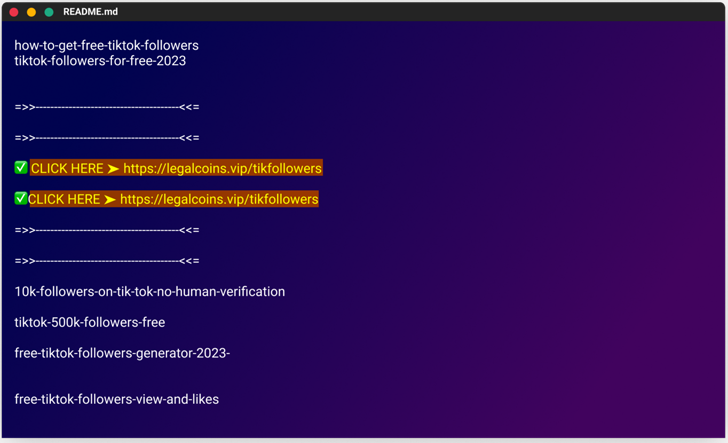
The modus operandi involves poisoning the registry with rogue packages that include links to phishing campaigns in their README.md files, evocative of a similar campaign the software supply chain security firm exposed in December 2022.
The fake modules masqueraded as cheats and free resources, with some packages named as “free-tiktok-followers,” “free-xbox-codes,” and “instagram-followers-free.”
The ultimate goal of the operation is to entice users into downloading the packages and clicking on the links to the phishing sites with bogus promises of increased followers on social media platforms.
“The deceptive web pages are well-designed and, in some cases, even include fake interactive chats that appear to show users receiving the game cheats or followers they were promised,” Gelb explained.
The websites urge victims to fill out surveys, which then pave the way for additional surveys or, alternatively, redirect them to legitimate e-commerce portals like AliExpress.
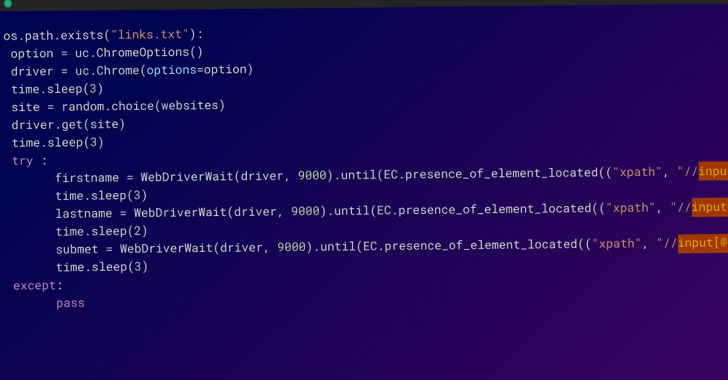
The packages are said to have been uploaded to npm from multiple user accounts within hours between February 20 and 21, 2023, using a Python script that automates the whole process.
What’s more, the Python script is also engineered to append links to the published npm packages on WordPress websites operated by the threat actor that claim to offer Family Island cheats.
This is achieved by using the selenium Python package to interact with the websites and make the necessary modifications.
In all, the use of automation allowed the adversary to publish a large number of packages in a short span of time, not to mention create several user accounts to conceal the scale of the attack.
“This shows the sophistication and determination of these attackers, who were willing to invest significant resources in order to carry out this campaign,” Gelb said.
The findings once again demonstrate the challenges in securing the software supply chain, as threat actors continue to adapt with “new and unexpected techniques.”