The threat actor known as UAC-0099 has been linked to continued attacks aimed at Ukraine, some of which leverage a high-severity flaw in the WinRAR software to deliver a malware strain called LONEPAGE.
“The threat actor targets Ukrainian employees working for companies outside of Ukraine,” cybersecurity firm Deep Instinct said in a Thursday analysis.
UAC-0099 was first documented by the Computer Emergency Response Team of Ukraine (CERT-UA) in June 2023, detailing its attacks against state organizations and media entities for espionage motives.
Beat AI-Powered Threats with Zero Trust – Webinar for Security Professionals
Traditional security measures won’t cut it in today’s world. It’s time for Zero Trust Security. Secure your data like never before.
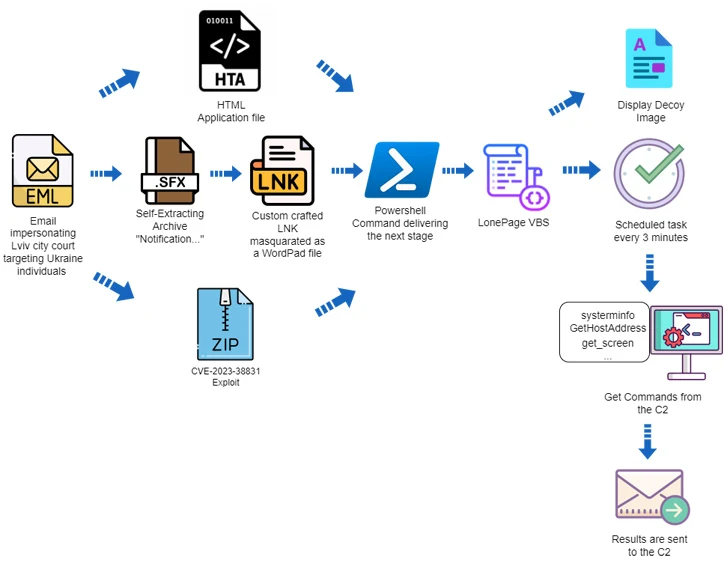
The attack chains leveraged phishing messages containing HTA, RAR, and LNK file attachments that led to the deployment of LONEPAGE, a Visual Basic Script (VBS) malware that’s capable of contacting a command-and-control (C2) server to retrieve additional payloads such as keyloggers, stealers, and screenshot malware.
“During 2022-2023, the mentioned group received unauthorized remote access to several dozen computers in Ukraine,” CERT-UA said at the time.
The latest analysis from Deep Instinct reveals that the use of HTA attachments is just one of three different infections, the other two of which leverage self-extracting (SFX) archives and bobby-trapped ZIP files, which exploit the WinRAR vulnerability (CVE-2023-38831, CVSS score: 7.8) to distribute LONEPAGE.
In the former, the SFX file houses an LNK shortcut that’s disguised as a DOCX file for a court summons while using the icon for Microsoft WordPad to entice the victim into opening it, resulting in the execution of malicious PowerShell code that drops the LONEPAGE malware.
The other attack sequence uses a specially crafted ZIP archive that’s susceptible to CVE-2023-38831, with Deep Instinct finding two such artifacts created by UAC-0099 on August 5, 2023, three days after WinRAR maintainers released a patch for the bug.
“The tactics used by ‘UAC-0099’ are simple, yet effective,” the company said. “Despite the different initial infection vectors, the core infection is the same — they rely on PowerShell and the creation of a scheduled task that executes a VBS file.”
The development comes as CERT-UA warned of a new wave of phishing messages purporting to be outstanding Kyivstar dues to propagate a remote access trojan known as Remcos RAT. The agency attributed the campaign to UAC-0050.