New evidence shows that Iran’s intelligence and military services are associated with cyber activities targeting Western countries through their network of contracting companies.
A string of multi-year leaks and doxxing efforts led by anti-Iranian government hacktivists and dissident networks has uncovered an intricate web of entities associated with the Islamic Revolutionary Guard Corps (IRGC) involved in cyber-attacks and information manipulation campaigns.
Cyber threat intelligence provider Recorded Future discussed some of the findings in a new report, published on January 25, 2024.
It has been found that at least four intelligence and military organizations linked to the IRGC engage with the bulk of cyber contracting parties. These include:
- IRGC’s Electronic Warfare and Cyber Defense Organization (IRGC-EWCD)
- IRGC’s Intelligence Organization (IRGC-IO)
- IRGC’s Intelligence Protection Organization (IRGC-IPO)
- RGC’s foreign operations group, aka the Quds Force (IRGC-QF)
“Each body has had specific advanced persistent threat (APT) groups closely associated with them; for example, in 2022, the Nemesis Kitten APT Cobalt Mirage, UNC2448, TunnelVision, and Mint Sandstorm (formerly tracked as “DEV0270”) was linked via personas to the IRGC-IO by the anti-government group Lab Dookhtegan,” the report explained.
The leaks analyzed by Recorded Future show that these agencies maintain a long-standing relationship with Iran-based cyber contractors. Public records also point to an ever-growing web of front companies connected via individuals known to serve various branches of the IRGC.
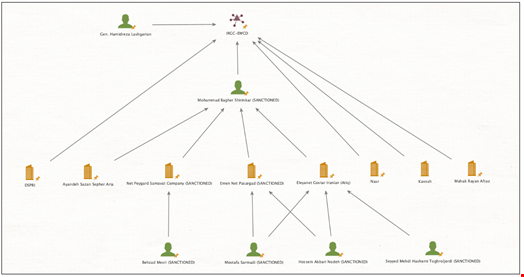
Some of these cyber operators involved in offensive cyber activities include “Ayandeh Sazan Sepehr Aria Company,” “Sabrin Kish,” “Soroush Saman Company” and other sanctioned entities like “Najee Technology Hooshmand Fater LLC” and “Emen Net Pasargad,” Recorded Future reported.
However, researchers have noticed constant movement within the web of Iran-based cyber contractors, with companies frequently disbanding and rebranding in an attempt to obfuscate their activities.
“We have observed overlaps between personnel members, regularly referred to as ‘board members,’ who share roles in different contracting companies. Some of the data reveals names of high-ranking IRGC officials purportedly responsible for leading and coordinating Iran’s offensive cyber ecosystem,” Recorded Future researchers wrote.
Involved in the 2020 US Presidential Election Manipulation Campaigns
Through their links with these cyber contractors, the abovementioned Iranian government agencies are associated with, if not directly complicit in, the targeting of major US financial institutions, industrial control systems (ICS) in the US and around the world, and ransomware attacks against various industries, including healthcare providers like children’s hospitals.
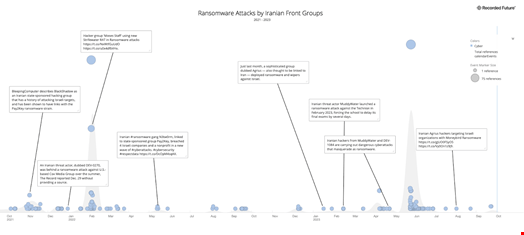
They also combine information operations with cyber intrusions to foment instability in target countries. For instance, some of these contractors were involved in targeting the 2020 US presidential election.
Finally, it has been shown that some of these contractors export their technologies abroad, both for surveillance and offensive purposes.
The leaks show that IRGC-related cyber offensive infrastructure has been used to deploy financially motivated attacks, for example.
Finally, based on those leaks, Recorded Future researchers concluded that US government sanctions are likely proving to be an effective legal and diplomatic tool, making it harder for cyber companies under the IRGC umbrella to evade detection.
“It is likely these efforts also adversely affect contractors’ abilities to openly recruit new and skilled labor,” reads the report.
Read more: Iranian Threat Group Hits Thousands With Password Spray Campaign
